Mistake 1 – Not locking down the right ports for convenience.
There are many differences between AWS and Microsoft Azure, not least in the terminology they use. For instance, Microsoft uses the term VMs for virtual machines, whilst over at Amazon the term for virtual machines are ‘instances’.
Microsoft uses the term ‘security group’ to mean a group in which members have all the same set of permissions. For example, a security group can all have access to the same files or folders. In AWS speak, a security group represents a firewall. When you create an Elastic Compute Cloud (EC2) instance, AWS creates a new security group, its sole purpose is to manage access control to that specific instance.
Before you lock down access to an instance, deciding which security groups are assigned to which instances is a must. Each security group can be programmed with its own set of inbound and outbound rules. I.e. It’s essential to make sure security groups are properly arranged because it’s not uncommon to leave some groups unprotected. Slip-ups like this are similar to when people made sure the windows are locked but then leave the front door wide open.
Mistake 2 – Providing more than the minimum permission set.
The accessibility of cloud servers is a major benefit for users but it can equally be a major point of weakness. Anyone with the right authorisation can enjoy the convenience of accessing the cloud servers from practically anywhere, but that same feature is what makes it prone to hacks at the same time.
Access control and management of the cloud data is a fine balancing act, between allowing users access to the applications and information while keeping the data safe from security breaches. Certain restrictive data environments can keep your data safe, but prevent your users from doing their jobs. Our recommendation is to adopt the principle of least privilege as best practice for your organisation – especially when creating security politics or IAM policy groups for external contractors, 3rd party applications or other teams.
Mistake 3 – Not encrypting sensitive data in transit or at rest
Essential computer data encryption
It’s a fact your sensitive information is always vulnerable to hackers’ attacks, even if you’re on a private network accessing a private cloud. Data breaches can happen and the trick is to minimise the risk using well-architected frameworks and working with an IT partner who follows security and governance best practices, even better if they are ISO 27001 certified and Cyber Essentials Plus verified.
Many security breaches happen due to poor password management or employee mistakes. It’s crucial to protect your cloud data by encrypting it, whether in transit or not. When choosing a cloud vendor, always bear in mind their best practice regarding data encryption as this is a proven way to make data useless to those who might try to breach it.
Many enterprise applications are hosted in the cloud today. While businesses are required to protect their information, they are relying on a cloud service provider that either allows the customer to encrypt the data before it reaches cloud storage, or includes a (SaaS) provider that can encrypt and decrypt the data for them.
Certain CRM applications, such as Salesforce, and enterprise file sync and share apps, use secure web connections. Transport layer security encryption or simply TLS transfers data from user’s keyboards or servers to desired web applications. Cloud storage apps, also allow their users to create secure links between their network and the cloud storage. When the data reaches the MSP’s cloud, the application provider does the encryption and secures the data at rest. It’s also working making sure the encryption or decryption at the load balancer level is correctly configured.
Mistake 4 – Not using multi-factor authentication for your users.
Cloud applications may use password authentication alone to protect the sensitive data stored in the cloud. Considering the known weaknesses of passwords, this is not the best solution. Some cloud service providers offer multi-factor authentication (MFA) to increase the security of data in the cloud. However, using various tools to secure data may create needlessly complicated login procedures for users and IT departments.
If your business uses cloud apps such as Microsoft Office 365 or Salesforce, there’s a big chance they are primarily password-protected. Worrying as a recent report from Verizon reveals that 81% of hacking data breaches are password-related. This should be a cause for concern if your cloud platforms all have different access policies and password requirements.
Multi-Factor Authentication can reduce the risk of data breaches.
MFA solution integrated with all your enterprise cloud applications can secure access in two ways:
1) by adding another layer of authentication so that users can prove their identity
2) by providing visibility to the IT security teams of who is accessing the apps they are managing
Finally managing cloud app security is much easier when there is just one MFA solution protecting it across multiple applications.
Mistake 5 – Not running a fire drill for when the sh*t hits the fan.
Run a fire drill for when you have a data breach within your company
Last but not least, securing your data physically is crucial for any business. If you keep your servers in data centres, what kind of security protocols are in place to monitor who has access to the servers and thus avoid unwanted intrusions? Are your data servers secure enough?
Do you have a company fire drill plan in place? These are essential should you ever have the misfortune to experience a data breach. The purpose of a fire drill is to prepare for the real thing. Everyone should know what to do and how to handle a data breach – but how many have trained for it? In those crucial hours, do your employees know how to recover data and have you discussed a disaster recovery plan with your MSP to identify recovery point objectives? It’s how you respond to these events that make the difference as every second counts and the longer it lasts, the worse the damage not only to your business but also to your professional credibility. If you don’t already have one in place, a security protocol is another must; to wipe down or lock away your devices if they are stolen or lost. A data breach can be devastating to any business, but avoiding these mistakes reduces the chances of you falling victim to cyber-criminals.
These mistakes are commonplace and largely overlooked until a cyber-attack actually happens. And when it does happen, data intrusions can often have a devastating impact on businesses.
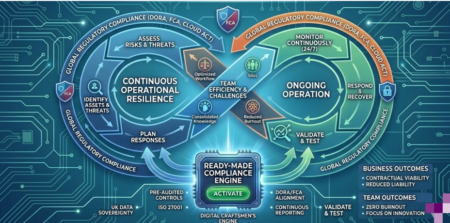
Order a free vulnerability scan with us
However, you do not have to be at risk, simply sign up for a free vulnerability scan with Digital Craftsmen now, and in return we’ll deliver you an up to the minute report assessing your current state of vulnerability, calling out potential issues – and we go one step further by providing recommendations of what to do to increase your security level. Our reports are powered by our partnership with Qualys, the industry leader in vulnerability scan software.
In short, our report provides you with peace of mind about your business security, so with nothing to lose – sign up here now:
For further information about the vulnerability scan services we offer, visit our website by clicking here. Contact our Craftsmen on +44(0)20 3745 7706 or email them at [email protected]