Running a security audit on your IT infrastructure means you’re one step ahead of hackers
‘Audit’ is a word laden with significance, impact, gravitas, formality and consequences. And, we freely admit they are frequently slanted towards the negative side of the fence – audits are often seen as a threat, an intimidating challenge. Actually an audit will help you avoid a Judgement Day, by reviewing and understanding the state of your infrastructure you are able to avoid any potential security incidents. It’s a tool to collect information used to plan and execute changes to your infrastructure to make it more secure, to improve on it. Let’s have a look at what that entails Despite its potentially negative semantics, we use the term ‘audit’ to mean the security and vulnerability reviews follow a well developed and structured formal process. This ensures no nooks and crannies are overlooked and all audits are performed to the same high standard. It is as simple as that. There are many ways to carry out vulnerability and security audits, and quite a few aspects may be involved. Our approach to vulnerability scanning is solution-oriented tailored specifically for the needs of our customers. A secure IT workload needs to address five domains of IT security architecture:
- Identity and Access Management – Identify who and which services are allowed to access your system, with which privileges, and the levels of authentication required for each of the identified principals
- Monitoring and Detection – Having components in place that monitor, analyse and detect what is happening in your infrastructure, is important for protecting your infrastructure and the data you handle and process in it. Intrusion Detection Systems, Firewalls, and other systems are well-known tools.
- Infrastructure protection – Compartmentalise your infrastructure and IT workloads into smaller, well-defined elements with clear access and communication pathways between them so as to avoid cross-contamination and smaller “blast radii” of any potential security breach you may encounter
- Data protection – Not only PII (personally identifiable information, in relation to GDPR) must be protected and held securely and safely, any kind of business data you are storing and processing is at stake here. Data at rest and in transit needs to be protected from prying eyes, and recovery in case of data loss or disaster must be planned, tested, and automated.
- Incident Response – What are you going to do in case of a security breach or incident? What do you do if you detect a “smoking gun”? How do you contain the incident, or prevent any further data leakage? Which tools and process do you have in place?
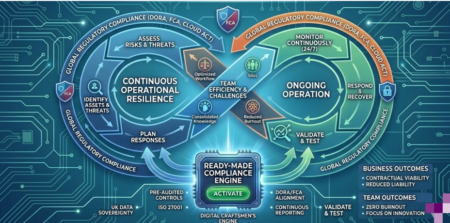
Having only scratched the surface a little, there is a lot usually to be done in each of these five domains – and it quickly gets very confusing what set of security and vulnerability tests and analyses are necessary or desirable for your user case. Therefore, we have packaged up well-defined sets of scanning and testing profiles based on typical use cases. Do your workload(s) fall into any of these categories?
- Vulnerability Scan – A surface scan of your IT estate or workload, seeking to detect any known vulnerabilities. This is a multi-purpose set of scanning and probing tests applicable to all types of IT workloads. Run as a black-box text, no internal probing or analysis of your data and applications is necessary. We then discuss the actionable report with you and monitor progress with a series of subsequent scans with the same profile.
- PCI Vulnerability Scan – Are you storing, processing or otherwise in contact with financial and credit card data? Then this scanning profile ensures that your system is compliant with the provisions and requirements of the PCI standards (e.g. PCI DSS, P2PE, 3DS etc).
- Deep Vulnerability Scan – Executed as a white box test, deep vulnerability scans also cover checking misconfiguration of access rights for file systems, common web application misconfiguration scenarios, vulnerabilities for SQL-Injection and XSS (cross-site-scripting) and other common sources of IT vulnerabilities.
We are not covering everything in our pre-packaged vulnerability scan offerings – nor should we (or anyone else for that matter) as that is rarely necessary, if at all. However, we also conduct bespoke custom vulnerability reviews that are tailored to your specific needs. In collaboration and agreement with you, these reviews can be as succinct or comprehensive as required, and deeper than the level of detail and coverage that pre-defined packages provide. Why bother, you might ask? The pandemic has changed the working landscape with many employees now working remotely. This has opened up the doors or vulnerabilties for hackers who are accelerating their cyberattacks so profitable has it become for them. Phishing and password mismanagement remain the two biggest entrypoints for cybercriminals to break in and steal data. Though now there is an extra twist in that they won’t launch an attack straight away, rather they will lurk and observe your passwords, names and identities for days or even weeks, whilst secretly loading malicious code until they launch their full attack by which time your IT infrastruture, systems and processes are fully compromised. Protecting your infrastructure does not stop with only enforcing strong passwords. It is an ongoing process to harden and secure your entire infrastructure in as many ways possible and required. And it all starts with a security and vulnerability scan. Why not give the Digital Craftsmen team a call to find out more about our ranges of services and consultancy we offer to businesses and start your New Year knowing your infrastructure and business are secured. Contact us on +44 (0)20 3745 7706 or email us on [email protected] Digital Craftsmen is verified by ISO 27001 and Cyber Essentials which means we can deliver services you can trust.