Many business directors resist the idea of bringing in third-party cyber security experts for cost reasons. They think it’s an added expense when they have their own IT team in-house to manage the risks.
However, as ransomware attacks are becoming more sophisticated and relentless, the time has come for directors to do a proper risk analysis of the threats to their business.
How to understand the costs of a ransomware attack?
In this blog, we help businesses understand the true costs of ransomware attacks and show how it makes financial sense to bring in third-party security experts and a SOC to secure your business.
How does one calculate the ROI of cyber security investments?
Traditionally, ROI is calculated based on returns on cost.
This equation however usually works for investments bringing positive results such as cost savings or revenue making activities. Cyber security is seen as a pre-emptive investment, and its ROI should be based on how much loss the organisation will avoid due to the investment.
Calculating Risk Reduction ROI
There will always be a financial cost in implementing cyber security and using this formula will help to determine the cost of potential risk versus the cost of control.
The most widely used formula is as follows:
ROI = (reduction in risk ‘£’ – cost of control)
____________________________________
Cost of control
This Formula Makes it Simpler to Understand the True Costs of Ransomware:
– for your organisation to review the cost of solutions per technical control
– to compare mitigation strategies and determine how the investment in expert third party security specialist SOC weighs up favourably against not having one
Understand the True Costs of Ransomware – Reputational Damage
As ransomware continues to dominate business and political news, it’s becoming a case of when not if your business is attacked by cyber-criminals for ransomware.
Directors need to weigh up damage to a company’s reputation when deciding to invest in cyber security, and how much that is worth to the business. Because being the weak link in a supply chain, or losing personal client data to the dark web will be seen as irresponsible. The consequences of that are immeasurable as clients lose confidence and take their business elsewhere to competitors.
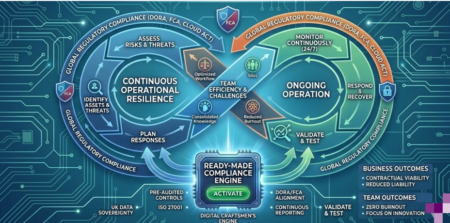
Outsourcing SOC to third-party cyber security experts
We talk about economies of scale in our SOC as a Service page and Cyber security as a service blog post, and with good reason. It’s the most cost-effective way for small to medium-sized businesses to access the talent, specialist software and always-on monitoring needed. All this is supported by a rapid response team looking for any anomalous activity or incident, trained to respond immediately following the * 1-10-60 rule when any threat is detected. Ask your current cyber security team if they offer the 1-10-60 level of protection, and if they don’t, then start considering your options – fast. If you’re not sure what to ask your technical team about raising the levels of cyber security in your business, this white paper from NCSC provides valuable insights on what to consider in your planning against ransomware attacks.
It’s becoming clear that outsourcing to a specialist team of cyber security specialists not only makes financial sense, it equally shows directors have met their regulatory obligation in safeguarding data and client information.
Read our Cyber Security – Build it or Buy it guide with our cybersecurity partners Armor on how the financials really do weigh up in favour of bringing in third-party experts.
Find out how our ISO 27001 and Cyber Essentials verified team of cyber security experts are protecting businesses like yours – call us on 020 3745 7706 or email [email protected] to find out how.
* 1-10-60 rule – one minute to detect an attack, ten minutes to investigate and 60 minutes to remediate. Any longer and hackers can break-in.